Why Securing the Internet of Things is so Vital
3 May, 2016
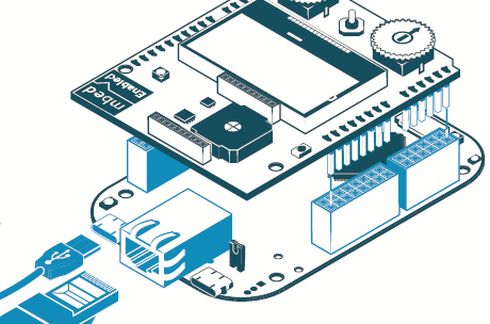
Not only software have to be secure, so does the hardware: This includes silicon production in the factory, hardware-based security in the chip and in the software

Not only software have to be secure, so does the hardware: This includes silicon production in the factory, hardware-based security in the chip and in the software
By: Coby Sella, VP Product and Technology IoT BU, ARM
The Internet of Things (IoT) is the most important buzzword of the day. From the Consumer Electronics Show, to Mobile World Congress, IoT is everywhere in the news, plastered on marketing materials, and headlining press releases. In some sense, the “Internet of Things” is today what the World Wide Web was in the ‘90’s.

A little bit of a Wild West egged on by visions of how the Internet could change the way we live.
As we know, the Internet has transformed society in ways that couldn’t have been predicted, and the mobile revolution has only made it more so by giving billions of people around the world instant, on-the-go access to friends, family, and services.
IoT is about Trust
But unlike the 1990’s, today we can better appreciate the need to build secure systems from the ground up, and IoT gives us the opportunity to do so. If we don’t, and worries about security slow IoT adoption, then we risk stalling further innovation in what could be the next wave of transformative applications.
By in large, the groundwork for the Internet of Things is already here. In fact, Gartner forecasts that 6.4 billion connected things will be in use by the end of 2016, and this number will reach 20.8 billion by 2020. Today, tiny, low energy, yet ever more powerful compute engines, radio and sensor technologies are bringing intelligence closer to the edge of the proverbial network.
This enables developers to build context aware systems that can interact with their immediate environments. Add to that the ability for systems to communicate with each other, either over a small Bluetooth network or through the Cloud on a much larger scale, and the doors are open for an unimaginable number of useful applications.
We’re already seeing connected, smart farms, smart homes, smart toys, on the spot resource management, and ADAS-enabled vehicles. What we’ve yet to see is a consistent pattern of focus on security within the electronics industry and developer community.
Security Bottom Up
As IoT becomes more pervasive there will be more sharing of data than ever before, all coming from a range of different devices and systems, and it will in fact attain new levels of value. Therefore, protecting data will be paramount. This isn’t to say no one is concerned, or working on the problem today, but given the broad attack surface that IoT affords would be hackers, it means that more work needs to be done to ensure all points in the IoT chain are protected and trusted.
It is important that security will be designed and embedded into these systems from the start, not as an afterthought. It has to be easy to deploy so that the company making athletic shoes, for example, can implement security as easily as the company producing the servers. This is a top priority at ARM. It presents an intellectual challenge not only for our own engineers to solve, but an opportunity for the industry at large as well.
Not only does software have to be secure, so does the hardware architecture. This includes silicon production in the factory, implementing hardware-based security in the chip, and creating a foundation of security in the software. This means protecting the device, the communication layer, and allowing management of the system through lifecycle security, and communications security that includes encryption, authentication, and over-the-air updates. Device integrity is at play here too, which includes secure identity, software identity and isolation.
The unknown scaling
Developers need to think about technologies that will help systems scale. For example, a streetlight today manages light, but tomorrow it may be a gateway feeding in weather data, traffic conditions, even triangulating the noise of a gunshot in a city. Finally, systems must be thoroughly tested for vulnerabilities before they are deployed.
One of the best things systems developers can do is to hire people with good hacking skills who can test out systems before they are let out to the wild. To learn more on how to secure IoT, read the GSMA’s new IoT security guidelines released at the recent Mobile World Congress is a must read for anyone in service ecosystems, endpoint ecosystems, and network operation.
Today, it is already possible to architect security into a systems, and we can clearly establish a root of trust as demonstrated already in the smartphone and tablet world. These experiences enable us to create the foundation for many more services and things that can empower peoples’ lives, while providing new opportunities for innovation and development for our industry so that IoT fulfil its true potential and not fall into the dustbin of buzzwords.
Posted in: News , Security , Semiconductors



